One of the most common challenges we hear from executives responsible for protecting their industrial operations is an inherent lack of visibility of industrial control systems (ICS) and operational technology (OT) assets. These organizations lack visibility into connected assets, visibility into network communications, visibility into threat activity, and visibility into which systems are most vulnerable. Even harder when their environments are highly distributed, reliable, and timely rollups of useful information becomes both more important and more difficult.
Introducing the Dragos Platform CentralStore
We’ve been working for some time now with customers who operate in some of the most regulated and architecturally complex scenarios imaginable. This collaboration has resulted in a new offering we are pleased to introduce – the Dragos Platform CentralStore. The CentralStore aggregates multi-site data collected and analyzed from multiple Dragos Platform SiteStores. It brings OT cyber visibility, detection, and response to companies who don’t want to compromise operational effectiveness for operational efficiency at scale.
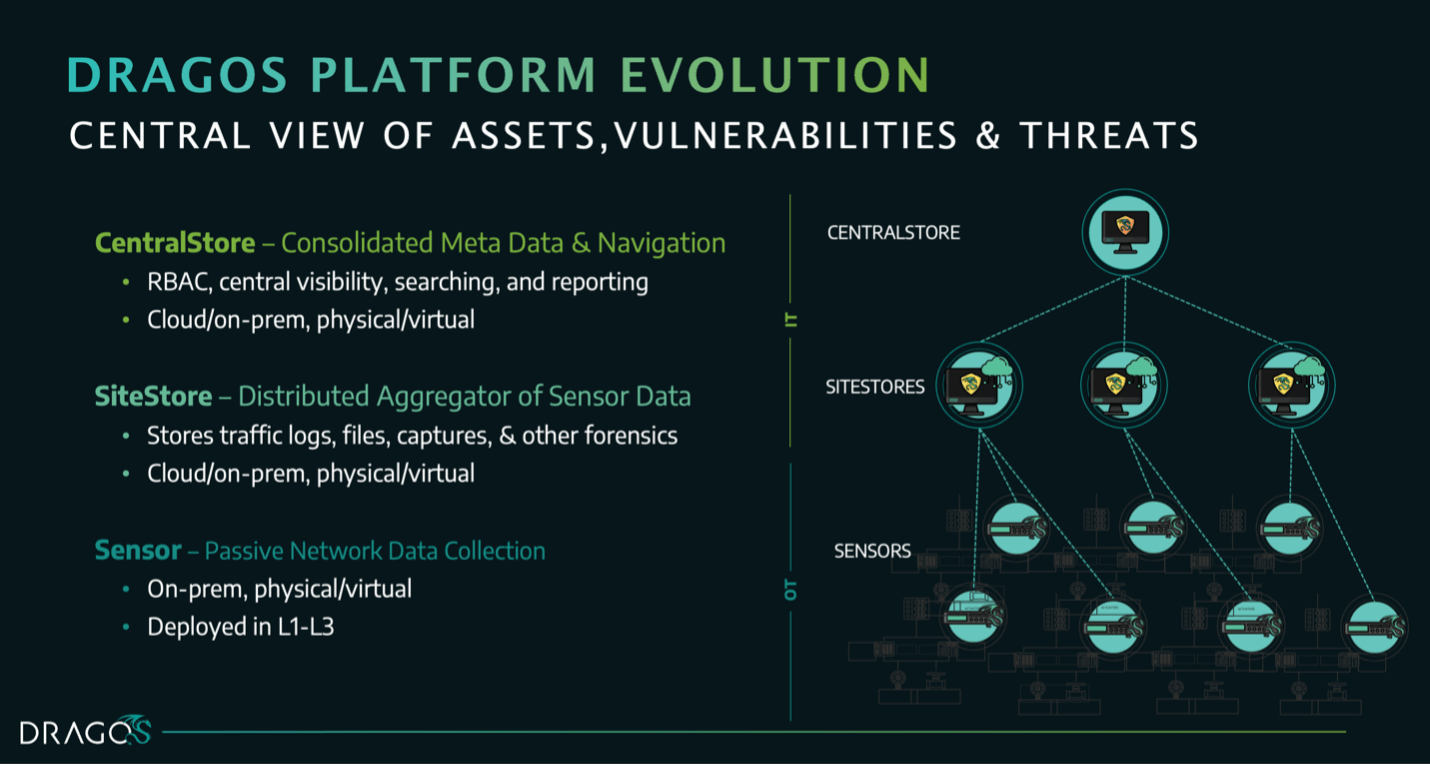
As of today, CentralStore is available and can be licensed for multiple connected Dragos Platform SiteStores, each of those engineered to handle industry-leading levels of monitored traffic. You can hear more about the CentralStore along with other recent improvements and enhancements we have made to the Dragos Platform in our upcoming webinar on Thursday, October 13, 2022.
The Dragos Platform – OT Visibility, Detection, and Response
For those who aren’t familiar with some of the powerful capabilities the Dragos Platform provides, here’s a quick summary:
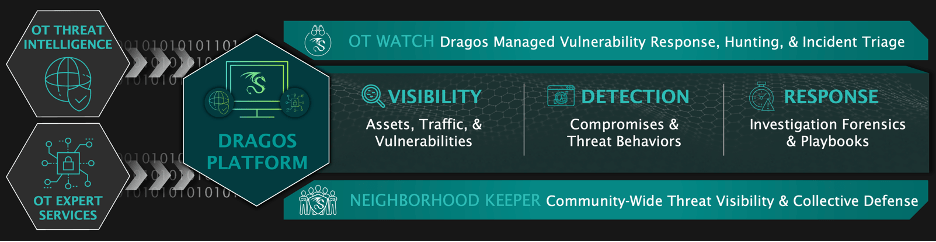
We incorporate the intelligence and expertise of one of the largest teams of OT cybersecurity practitioners anywhere which includes ICS/OT specific malware analysts, threat hunters, and field consultants doing regular assessments in customer environments on a daily basis. All of this insight is codified into the Dragos Platform in a number of ways but is generally aligned to three main areas: visibility, detection, and response.
Asset Visibility and Network Communications
Improve the accuracy and understanding of devices in your environment with the Dragos Platform through “operations safe” data collection and device-level detail including OT vulnerability intelligence.
The Dragos Difference:
- Full support across primary and strategic industrial vendors, equipment, and protocols
- Monitor for remote connections, search historical activity
- Step back and forth through timeline views to spot unexpected activity
- Group assets in a visual map with customizable zones for easier cyber-ops management
- Establish asset profile baselines for connected integrations with firewall and CMDB systems
Visibility is a broad category and one in which we include assets, network communications, and vulnerabilities because of how tightly related they all are. We believe that good OT visibility is foundational to effective threat detection and incident response. Without accurate information on the assets in your environment and how they’re communicating, you’re less likely to correctly detect suspicious activity.
OT Vulnerability Intelligence
Effective vulnerability identification becomes much less efficient if scarce resources are spent on remediation for something that was detected as a false positive or given higher priority than it deserved. Adverse supply chain risk may result from embedded vulnerabilities that go undetected. Older equipment and outdated inventories result in systems drifting out of compliance with corporate and regulatory standards, especially when manual methods and tribal knowledge keep information locked up in inaccessible locations. Users need accurate and useful insight within their own environments.
The Dragos Difference:
- OT specific analysis, correction, and enrichment of known vulnerabilities as well as Dragos identified vulnerabilities
- Alternative vulnerability mitigation advice, prioritized with “Now, Next, Never” guidance
- Disposition tracking for full vulnerability lifecycle management and to simplify audits
OT Threat Detection
The most effective platform for intelligence-based OT threat detection – as evidenced in the MITRE ATT&CK for ICS evaluation, to help defenders quickly orient to the most urgent and immediate threats in their ICS/OT environments.
The Dragos Difference:
- Both discrete and composite detections from analysis of threat groups TTPs and attacks updated regularly through Knowledge Packs
- Expertly curated Indicators of Compromise (IOCs), malicious IPs, domains, and hashes from the Dragos Intelligence team
- Anomalous traffic pattern identification and baseline deviation alerts which can be assigned for investigation
Investigation and Response
Giving responders the insight and tools to triage and investigate potential incidents using the Dragos Platform.
The Dragos Difference:
- Investigation response playbooks with OT-centric guidance from Dragos industry experts
- Collect and organize evidence by case in the analyst investigation workbench
- Centralized forensics and unique timeline views to coordinate across OT and IT teams
The Dragos Platform in Action – Beyond the Customer’s Walls
Customers who don’t have the skills or resources in-house to fully utilize asset visibility and threat detection built into the Dragos Platform can optionally add on the Dragos OT Watch managed service to their subscription which provides direct access to a global team of threat hunters who support triage and investigation on behalf of the customer. Certain roles and organizations also depend on broader visibility across a trusted community to know if the conditions and activity they are seeing is consistent with normal operations. With this in mind, customers who use Dragos Platform also have free access to our collective defense and community visibility technology – Dragos Neighborhood Keeper.
Customer Examples – Dragos Platform in Action
I love hearing stories from the field about how our customers are using the Dragos Platform to solve everyday OT cyber challenges, helping their teams do their work easier and with greater efficiency. Sometimes these little visual snapshots involve a discrete task that an OT cyber analyst might do repeatedly day-in and day-out. Other times it could be a major update that gives a Fortune 500 CISO the insight they needed to protect their global environments.
Customer Example #1 – Faster CISO Level Vulnerability Insight
The cyber team at this Fortune 300 power generation company knew they needed to quickly respond to vulnerability notices when their CISO asked to understand if and where they are vulnerable. Prior to this, there was a lengthy research project leaving the CISO feeling they didn’t have a handle on real-time visibility. With this updated dashboard tailored for their environment, they can easily report back. Fast. Simple. Visible.
Customer Example #2 – Teaching Electrical Engineers What Attacks Look Like
One of our largest utility customers based in Europe trains their Commissioning Engineers on how the Dragos Platform is able to detect and identify attacks on the substations. They launch real attacks and then show the commissioning Engineers (not Security, not OT Engineering – the Electrical Engineers responsible for the substations) what an attack looks like on the devices, how it’s seen and tracked in Platform, and the impact of what that means to them in their role as Commissioning Engineers.
Customer Example #3 – Feeding Global Threat Activity to a Food & Beverage Cyber Team
This international food and beverage company deployed a sensor at one of their Asian facilities. Once onboarded and tuned, they had a few notifications that they asked one of our Technical Account Managers to help them triage. The alerts were related to a potential backdoor used by the Dragos threat group ERYTHRITE. It was relayed to the executives at their USA headquarters who were asking for updates on potential activity, no matter where in the world it was occurring.
The Dragos Difference – Our Industrial Cybersecurity Experts
Behind every one of these real-world examples lies thousands of hours invested by the Dragos Threat Intelligence and Professional Services teams who are shoulder to shoulder with our customers in the field, actively engaged in threat hunts, performing architecture reviews, reversing new industrial malware, or jumping on the next available flight when boots on the ground are needed for incident response. The collective intelligence and insight of these teams is fed back to the Product and Engineering teams and then made available within our Platform, through Worldview Threat Intelligence, and to the broader community – sometimes even at no cost. These groups at Dragos are enormously talented and dedicated to the mission, and I appreciate every one of them for their commitment to keeping the lights on and the water flowing.
Learn More About Dragos Platform Updates
Join us for a deeper dive into all of these areas and get a Dragos Platform overview in our webinar on Thursday, October 13th. Learn more about this event and register here.
You can also read more about these updates in the datasheets that describe: a summary of the Dragos Platform, available physical and virtualized Appliances, and our subscription model. View more about our platform at: dragos.com/platform.
Ready to put your insights into action?
Take the next steps and contact our team today.
