70% of all ransomware attacks targeted 638 manufacturing entities in 33 unique manufacturing subsectors.
Visualize, Detect, and Respond to Threats Against Your Manufacturing Operations
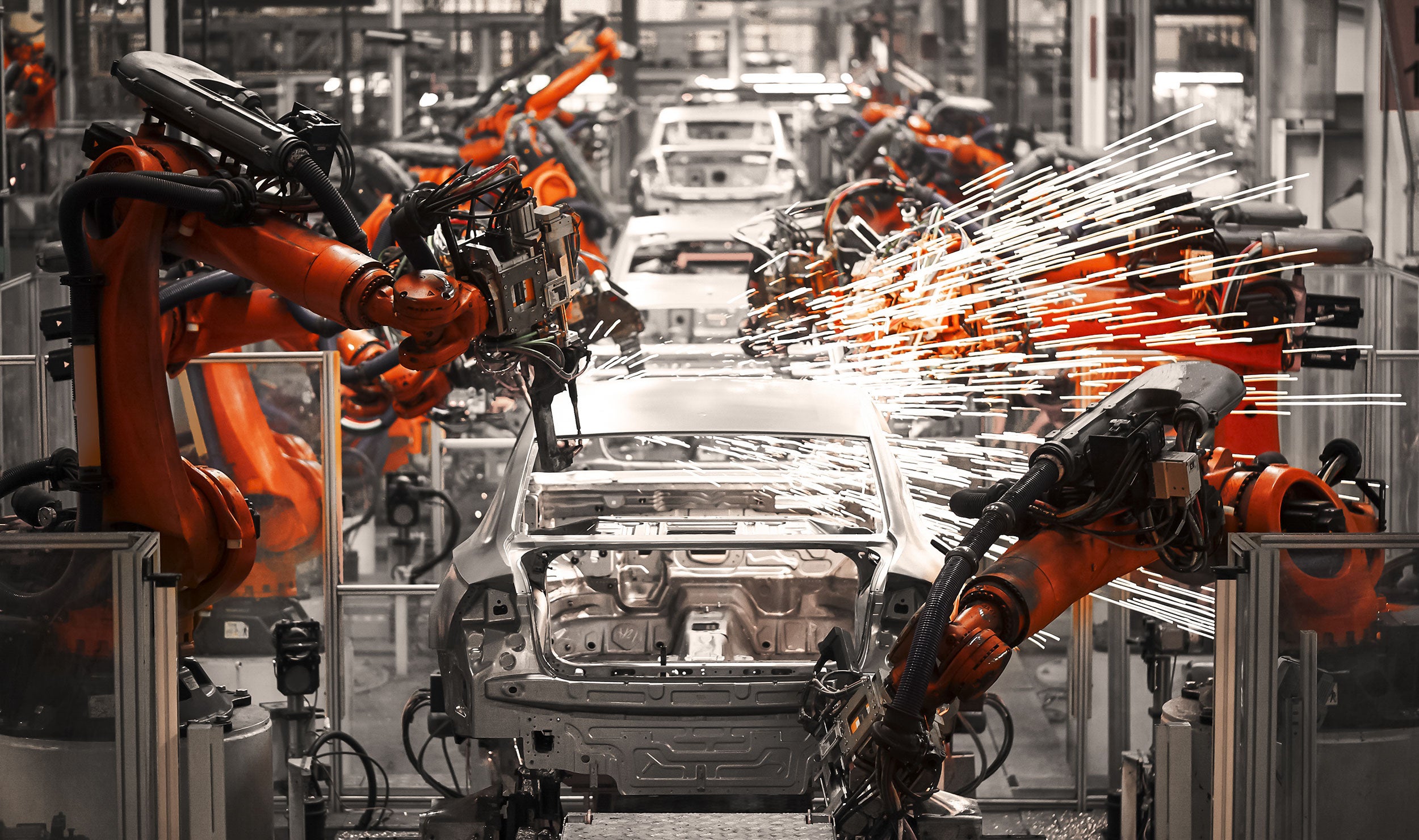
Rest easy knowing your operational infrastructure is in good hands.
The Dragos Platform utilizes deep packet inspection to give operators a complete picture of all connected OT equipment and network communications, from vendors like Rockwell Automation, Siemens, and Emerson. Your team will immediately benefit from in-depth visibility of assets and threats in your environment, along with playbooks to guide analysts step-by-step as they investigate potential incidents.
EXPLORE THE DRAGOS PLATFORMStay ahead of evolving threats.
The manufacturing sector has always been inherently global in nature, with supply chains spanning the world. This expanded attack surface makes it increasingly subject to the challenges of cyber risk, such as theft of intellectual property or disruption of production due to ransomware. Our world-class Threat Intelligence team distills adversary behaviors, tactics, techniques, and procedures into regular reports, so you can stay one step ahead of threats they pose to your operations.
MANUFACTURING THREAT REPORTPrevent Significant Breaches with Proactive Defenses.
Dragos’ professional cybersecurity services helps security and operations teams prepare for and respond to significant threats, no matter where you’re at in your journey. Our team will work with your staff on assessments, threat hunting, penetration testing, tabletop exercises, incident response, and training — either on-site or remotely.
PROFESSIONAL SERVICESKnown Activity Groups Targeting Manufacturing Operations
The manufacturing sector is a prime target for adversaries seeking to exploit industrial control systems environments. An attack can happen at any point across the major stages of operations. To help protect your infrastructure, Dragos tracks three activity groups specifically targeting manufacturing organizations and will continue to update this list as more information becomes available.

CHERNOVITE
Cyber threats don't wait _
Events & Webinars
MORE EVENTSJoin us on the frontlines with the latest webinars and events.










