Better Detection, Response, and Recovery from Cyber Events
50%
increase in attacks against industrial organizations
The Dragos Solution
Technology and services to defend your critical infrastructure.
Protect your assets and respond to threats against generation, transmission, and distribution systems — all in one place.
The Dragos Platform provides unprecedented visibility of assets and communications, knowledge of threats through intelligence-driven analytics, and prescriptive guidance via playbooks.
Gain in-depth visibility of threats electric systems face.
Receive pertinent reports via email or our online portal, and participate in live quarterly webinars with our deeply experienced team of threat intel analysts.
Attack electric sector cyber threats from all angles.
Our experienced Professional Services team can be dispatched to perform a variety of activities that allow you to fully understand your ICS environment, mitigate risks, and respond to threats confidently.
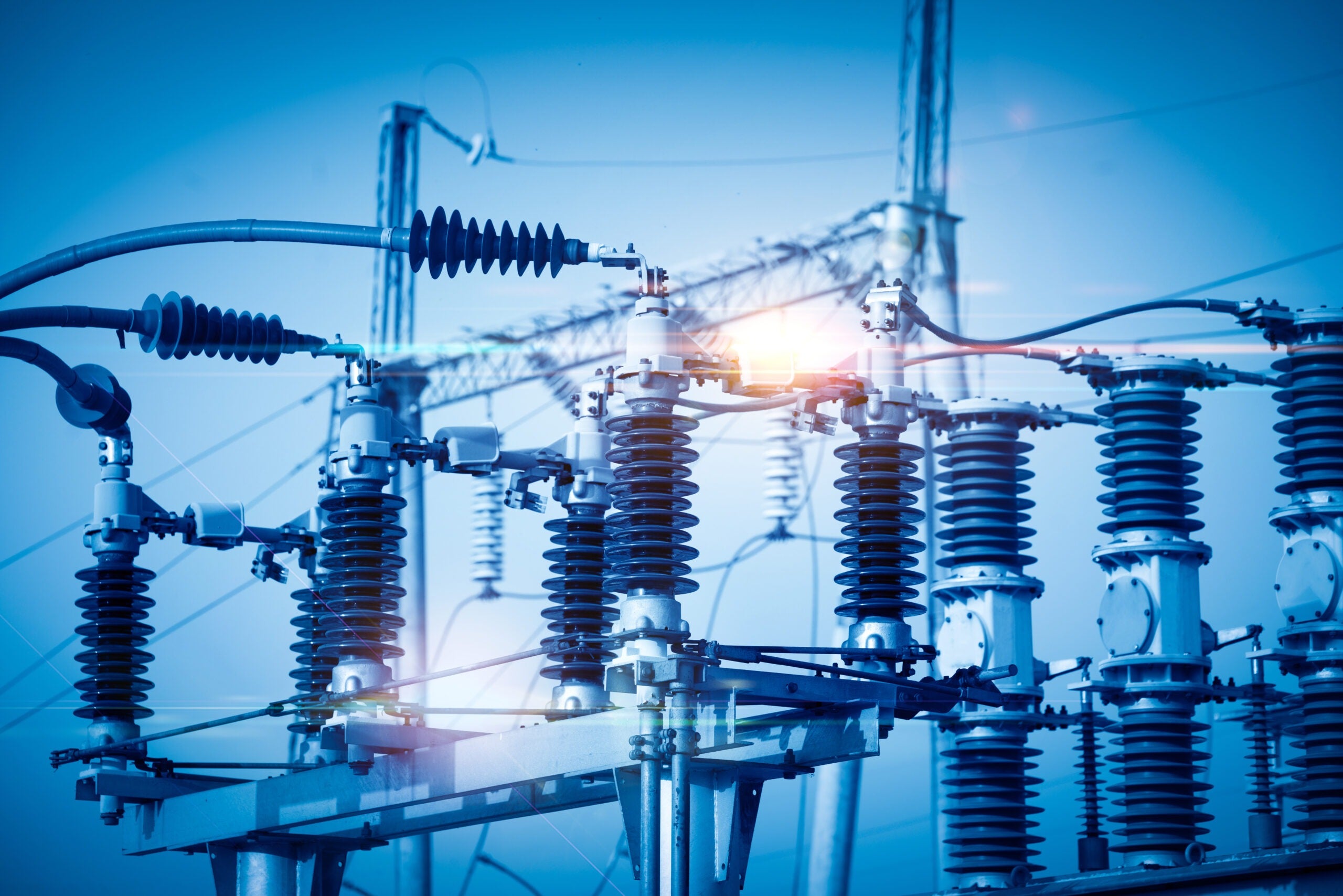
Industrial Strength Cybersecurity for Electrical Substations
The clear understanding Dragos has of the environment in which we operate allows us to cut through the hype around many potential industry vulnerabilities, so we can focus on the ones that matter most as we look after vital infrastructure and ensure supply to our customers.
Cyber threats don't wait!