Dragos made the annual cybersecurity pilgrimage to San Francisco, California on April 16-20 where each year thousands of people from the security industry gather for a week at the RSA Conference.
Dragos founder and CEO Robert M. Lee spoke about the importance of nuance in ICS and the risks of misattribution, adversary hunter Joe Slowik hosted a peer-to-peer session on threat profiling for network defense, and Dragos sponsored the ICS Village in the RSA Sandbox where a simulated ICS environment open to vulnerabilities showcased the Dragos platform.
Necessity of Nuance
“Hype has costs,” Mr. Lee told a packed audience on Tuesday. His talk, “Industrial Cyber Attacks: A Quest For Nuance With Lessons Learned From The Field,” highlighted the issues with overhyping industrial control system security threats and the consequences stemming from misunderstanding an increasingly active threat landscape.
Failure to appropriately communicate and report on ICS incidents can snowball into ineffective internal discussions and potentially make incident response difficult for defenders. Government and company leadership should consider the following questions before attributing cyber incidents within industrial control systems: How do you respond after publishing erroneous reports? What kind of consequences could false reports have?
Industrial infrastructures are among the most defensible networks around the world. Cyberattacks are difficult to execute and scale. “The threats are worse than we realize but not as bad as we imagine,” Mr. Lee said, but the threat landscape is still mostly unknown. The industry is not effectively collecting and analyzing data to determine the root cause of industrial cyberattacks, and the depth of activity of the adversaries.
Historically, methods to understand the threat landscape have relied on security vendors, incident responders, and governments analyzing through internet-connected sensors like firewalls and endpoint detection services. However, ICS threat detection can’t rely on traditional IT methods.
Mr. Lee said that over the next few years, the measurement of the threat landscape will hockey stick. This activity spike will be due to increasing threats, but also an increase in collection and analysis leveraging new tools, resources, and information-sharing.
ICS attacks are increasingly sophisticated. Dragos has analyzed three destructive malware samples targeting power generation facilities in 2015, 2016, and 2017. CRASHOVERRIDE, the malware attack that briefly took down electricity in Kiev, Ukraine in 2016 used legitimate protocols and functionality to disrupt the grid. And, even more troubling, the TRISIS attack against a petrochemical facility in Saudi Arabia last year targeted a safety system and was designed to cause harm and potential fatalities.
According to Dragos’ 2017 Year in Review, 64 percent of ICS-related vulnerability patches didn’t fully eliminate risk because the components were insecure by design, and 72 percent of ICS-related vulnerability advisories provided no mitigation guidance in addition to patching which suggests there is no method to reducing risk until after an update cycle.
Root Cause Analysis (RCA) is especially important to ICS environments, and poor RCA can lead to increased Mean Time To Recovery (MTTR) following an incident. To understand detection coverage, Dragos suggests mapping detection capabilities to each stage of the ICS Cyber Kill Chain and ensure analytical coverage across networks. By establishing and understanding a threat model, organizations can use it to create an intelligence-driven hypothesis that can be used to develop a threat hunt and incident response playbooks.
ICS-focused threat activity groups are becoming more prevalent and attacks are increasingly bold. To defend against the growing threat landscape and combat hype, Mr. Lee left the audience with one piece of advice: Do more, fear less.
A SOC in the Sandbox
Dragos sponsored the ICS Village inside the RSAC Sandbox to demonstrate how an attacker could leverage a home internet-connected camera to turn off a water pump in an ICS environment.
The ICS Village is designed to simulate threats in ICS environments, and how safety and security platforms, software, and human defenders identify threats and prevent attacks. The organization exhibits at a number of industry events including RSA and DEFCON.
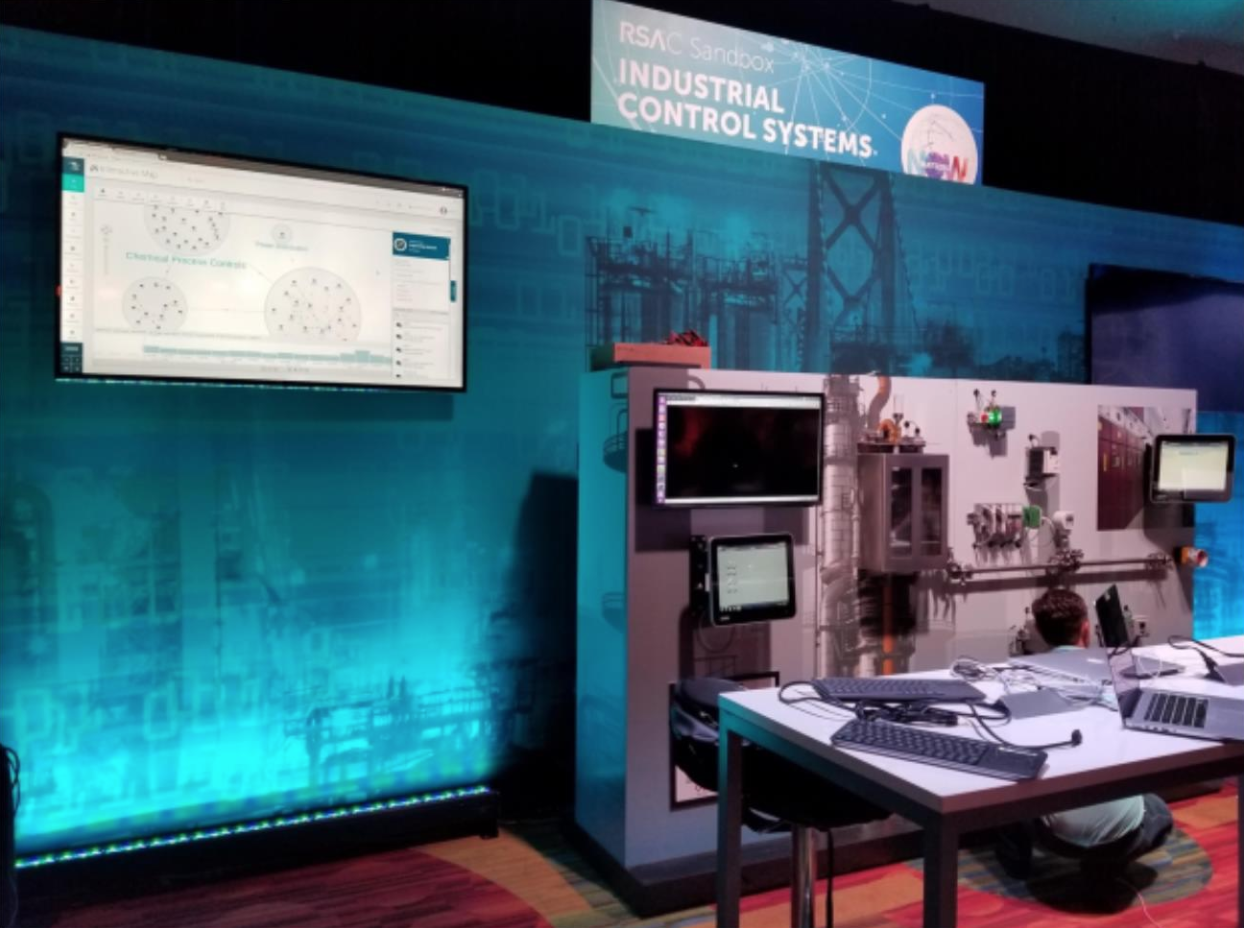
The village featured a smart home display full of IOT devices like a Google Home, garage door opener, and an IP-based camera. The interactive ICS Village demonstration panel next to the tabletop smart home contained a number of ICS components including programmable logic controllers (PLCs), human machine interfaces (HMIs), variable drives, water pumps, and switches.
In one theoretical attack scenario, a controls engineer who owned the home was unaware that his camera contained a vulnerability. A theoretical attacker leveraged the vulnerability to gain access to his corporate ICS network. The attacker scanned the home network and took over the engineer’s work computer. They waited for a VPN connection and then transferred an executable file to run on the computer within the control network and shut off the water flow.
The Dragos platform identifies and visualizes assets and activity on ICS networks, and in this scenario, the platform detected the malicious behavior between the compromised computer and the water pump. With the platform’s map of security zones, a defender can analyze activity between devices and analyze specific changes on individual assets. The platform operates as an operational technology security incident and event management system (SIEM) and can be deployed in a security operations center (SOC) model.
SOCs monitor networks, devices, applications, and servers and defend against threats. Thomas VanNorman, director of application engineering at the ICS Village led a discussion about SOCs in industrial control systems. He said each SOC should be a three-tiered system.
Tier one contains analysts who identify and escalate abnormalities. At tier two are incident responders who triage the events, analyze activity, and apply mitigations. Subject matter experts who dive deeper into analyzing threats and are closest to the process are on tier three. Unlike IT, threat detection in OT systems should be 100% either false positives or a detection. There is no room to leave detections unknown, Mr. VanNorman said.
The ICS Village demonstration panel is a valuable tool for practical exhibition of ICS assets, and Dragos will keep it at our offices in Hanover, Maryland.
Implementing Threat Profiling for Network Defense
Across from the ICS Village, Dragos’ Joe Slowik led a working session on threat profiling, focused on identifying threats to the organization and how to appropriately prioritize resources for defense. This session emphasized many key components of Dragos’ perspective on network security: Adopting a threat-centric approach to defense and response, and combining “self-knowledge” of operations with adversary information to develop appropriate security strategies.
In the session, Mr. Slowik started out by shifting attendees’ focus from external threats to internal sources of value: What parts of the defended network are important to an adversary, and how must an adversary reach these goals. This approach allows defenders to narrow the scope of potential threats to those most-relevant to the organization, while also identifying key resources and nodes that will likely feature in adversary operations.
After identifying sources of value and threats to those items, defenders can then begin developing a perspective of what countermeasures and visibility are necessary to respond to relevant threats. The entire purpose of this approach is to prioritize resources and focus defensive effort on those potential items that are both critical to the organization’s operations, and relevant to the organization’s likely adversaries.
Almost 40 people participated in the packed peer-to-peer session. Following the session, Mr. Slowik fielded requests to further the discussion and host future talks on the issues, which Dragos may incorporate into a future Dragos webinar.
Ready to put your insights into action?
Take the next steps and contact our team today.
