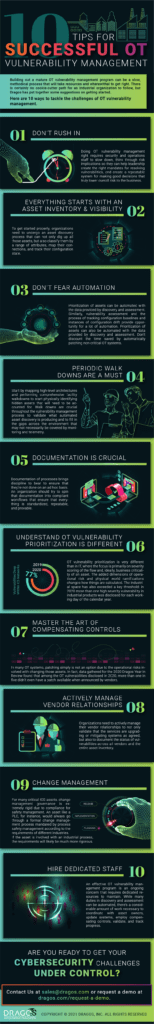
10 Tips for Successful OT Vulnerability Management
Industrial asset owners know that protecting the integrity of their systems is critical for maintaining operations, but the challenges around cybersecurity vulnerabilities make the job that much harder. As operational environments are increasingly connected and targeted by sophisticated attackers, sensible approaches to managing risk are needed more than ever. Get the top 10 tips for building a successful vulnerability management program in your OT environment in this infographic.
For an in-depth guide on approaching industrial vulnerability management, the whitepaper “Understanding the Challenges of OT Vulnerability Management and How to Tackle Them” is also available. Customers interested in how the Dragos Platform uniquely provides asset owners with the visibility and tools to manage OT vulnerabilities in their environments can read more here.
Download a printable 8.5 x 11 PDF version of the infographic by completing the optional form below.
View our next infographic
See the Dragos Platform in Action
Take the next step to protect your OT environment now with a free demo