Your first line of defense against adversaries
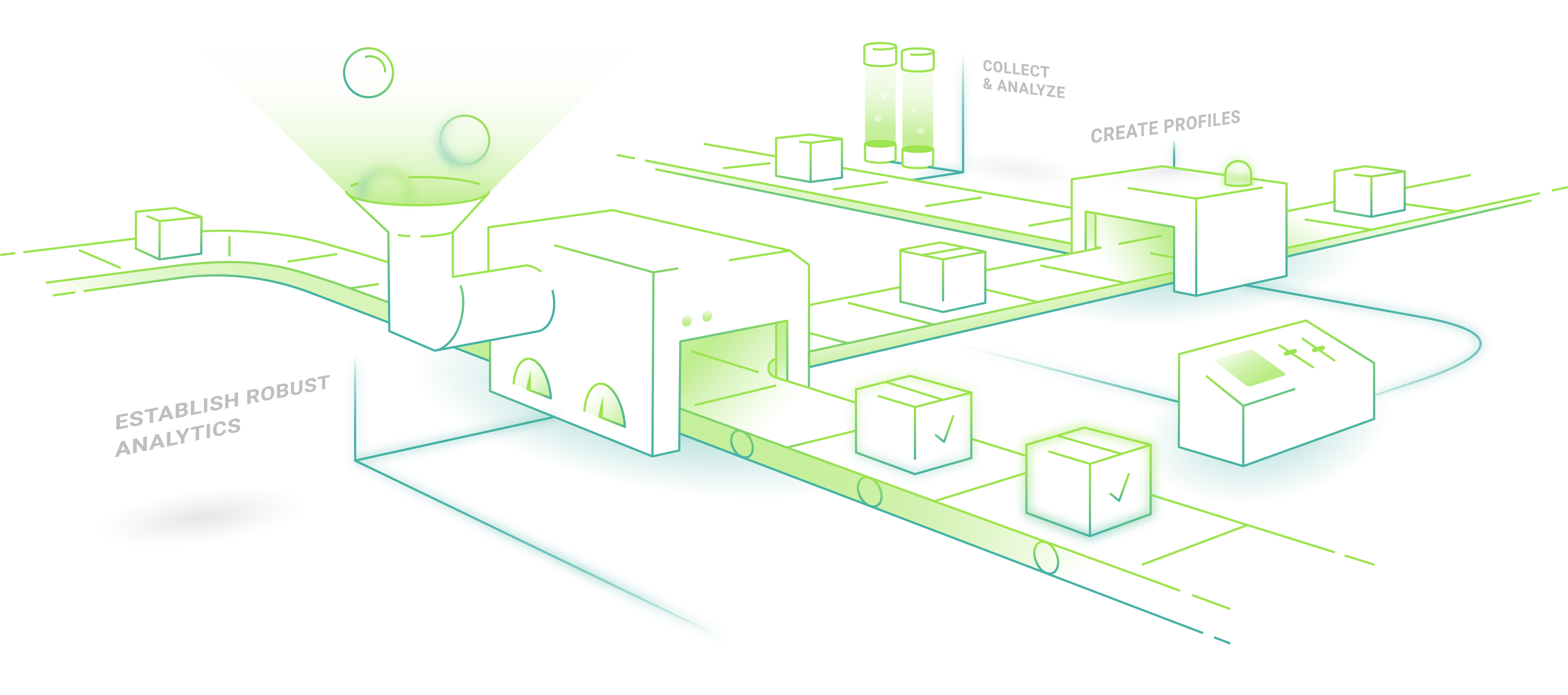
Powered by human intelligence, Dragos’ main threat detection method is based on analytics codified by our Threat Intelligence team. Our experts track adversary behaviors and extract their tactics, techniques, and procedures (TTP), which are then characterized into threat analytics we use to power the Dragos Platform’s accurate threat detection capabilities.
Learn how we classify threat groups.
Threat Groups We’re Tracking
The Threat Group reports below are compiled by our expert practitioners to provide awareness about your threat landscape and evolving threats, so you can create defensive plans to protect your ICS environments.

CHERNOVITE

KOSTOVITE

PETROVITE

DYMALLOY
Dragos Threat Intelligence
Want more in-depth visibility of adversaries, vulnerabilities and threats? Full reports detailing the tactics, techniques, and procedures (TTP) and Dragos’ research is available to our Threat Intelligence subscribers. Request a free 30-day trial today.

















